IT Administrator Diploma
Level 7 QLS Endorsed | CPDUK Accredited
583 Students enrolled on this course 5 (6 Reviews)
 Last updated January 1, 2024
Last updated January 1, 2024
Course Curriculum
| Software: | |||
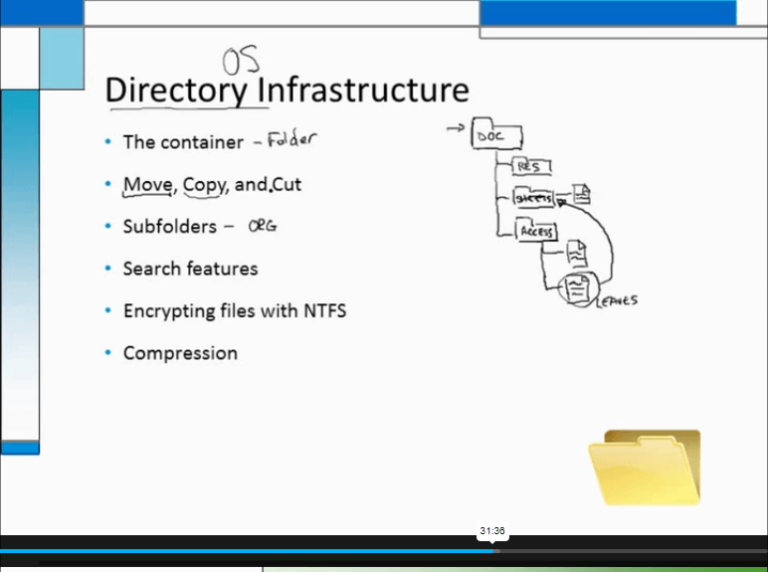
| What is an Operating System | 00:48:00 | ||
| Configuring the Operating System | 00:06:00 | ||
| What is an Application | 00:10:00 | ||
| Using Control Panel | 00:18:00 | ||
| Software and Concepts | 00:10:00 | ||
| Licensing | 00:06:00 | ||
| Using Software | 00:07:00 | ||
| Software Tools | 00:10:00 | ||
| Software | 00:14:00 | ||
| Hardware, Devices, and Peripherals | 00:06:00 | ||
| Hardware: | |||
| Hardware and Peripherals | 00:07:00 | ||
| Storage | 00:12:00 | ||
| Connectivity Devices | 00:05:00 | ||
| Network Components | 00:09:00 | ||
| Identify the Importance of Risk Management | 00:11:00 | ||
| Assess Risk | 00:13:00 | ||
| Mitigate Risk | 00:22:00 | ||
| Integrate Documentation into Risk Management | 00:14:00 | ||
| Classify Threats and Threat Profiles | 00:07:00 | ||
| Perform Ongoing Threat Research | 00:12:00 | ||
| Resources that Aid in Research of Threats | 00:03:00 | ||
| Implement Threat Modeling | 00:09:00 | ||
| Assess the Impact of Reconnaissance Incidents | 00:10:00 | ||
| Performing Reconnaissance on a Network | 00:07:00 | ||
| Examining Reconnaissance Incidents | 00:08:00 | ||
| Assess the Impact of Social Engineering | 00:10:00 | ||
| Assessing the impact of Social Engineering | 00:07:00 | ||
| Assessing the Impact of Phishing | 00:03:00 | ||
| Types of Wireless Attacks | 00:30:00 | ||
| Intrusion Monitoring | 00:08:00 | ||
| Wireless Security Risks | 00:22:00 | ||
| Authentication Attacks | 00:20:00 | ||
| Rogue Devices | 00:04:00 | ||
| Public Hotspots | 00:06:00 | ||
| Wireless Security Monitoring | 00:21:00 | ||
| Device Tracking | 00:17:00 | ||
| WLAN Security Infrastructure | 00:37:00 | ||
| Management Protocols | 00:23:00 | ||
| Other RADIUS Solutions | 00:15:00 | ||
| Security: | |||
| Introduction | 00:30:00 | ||
| Child Safety Online | 01:00:00 | ||
| Secure Payment Sites | 01:00:00 | ||
| Online Banking | 00:30:00 | ||
| How To Keep Your Password Safe | 00:30:00 | ||
| Common Scams | 01:00:00 | ||
| How I Got Pharmed | 01:00:00 | ||
| Virus Protection | 01:00:00 | ||
| Self Maintenance | 00:30:00 | ||
| Personal Information Online | 01:00:00 | ||
| Is The Internet Safe? | 00:30:00 | ||
| Importance of Cyber Security | 00:30:00 | ||
| Spyware Can Destroy | 00:30:00 | ||
| How Does Spyware Spread? | 01:00:00 | ||
| How To Remove Spyware | 01:00:00 | ||
| Anti Spyware Program | 01:00:00 | ||
| The Anti Anti-Spyware Programs | 00:30:00 | ||
| Research And Learn More | 00:30:00 | ||
| Choosing The Best Anti Spyware Tool | 01:00:00 | ||
| Computer Security And Spyware | 01:00:00 | ||
| The Programs To Avoid | 00:15:00 | ||
| Is It Legal? | 00:30:00 | ||
| Checklist Of Protection | 00:15:00 | ||
| The Information Security Cycle | 00:37:00 | ||
| Information Security Controls | 00:35:00 | ||
| Authentication Methods | 00:09:00 | ||
| Cryptography Fundamentals | 00:56:00 | ||
| Security Policy Fundamentals | 00:11:00 | ||
| Social Engineering | 00:31:00 | ||
| Malware | 00:25:00 | ||
| Software-Based Threats | 00:21:00 | ||
| Based Threats | 00:38:00 | ||
| Wireless Threats and Vulnerabilities | 00:43:00 | ||
| Physical Threats and Vulnerabilities | 00:09:00 | ||
| Manage Data Security | 00:47:00 | ||
| Manage Application Security | 00:56:00 | ||
| Manage Device and Host Security | 01:07:00 | ||
| Manage Mobile Security | 00:10:00 | ||
| A Risk Analysis | 00:17:00 | ||
| Implement Vulnerability Assessment Tools and Techniques | 00:04:00 | ||
| Scan for Vulnerabilities | 00:27:00 | ||
| Mitigation and Deterrent Techniques | 00:19:00 | ||
| Respond to Security Incidents | 00:23:00 | ||
| Recover from a Security Incident | 00:09:00 | ||
| Networking: | |||
| OSI Layers | 00:44:00 | ||
| LANs and WANs | 00:14:00 | ||
| Network Types | 00:07:00 | ||
| Transmissions | 00:36:00 | ||
| Cables | 00:41:00 | ||
| Fiber Optics | 00:16:00 | ||
| Converters and Connectors | 00:26:00 | ||
| Wireless Security | 00:15:00 | ||
| Authentication.prproj | 00:21:00 | ||
| Wireless Security Threats | 00:30:00 | ||
| TACACS | 00:10:00 | ||
| Keys | 00:26:00 | ||
| RADIUS | 00:06:00 | ||
| VPN Technologies | 00:16:00 | ||
| Tunneling Protocols.prproj | 00:05:00 | ||
| Acceptable Use | 00:59:00 | ||
| Common Problems | 00:32:00 | ||
| Troubleshooting | 00:28:00 | ||
| Network Technician Tools | 00:46:00 | ||
| Physical and Logical Issues | 00:19:00 | ||
| Open or Closed Ports | 00:09:00 | ||
| ARP Issues | 00:13:00 | ||
| Basic IT Literacy: | |||
| Core Concepts in Healthcare IT | 00:06:00 | ||
| EMR EHR Issues | 00:04:00 | ||
| Regulations, Standards, and Stakeholders | 00:13:00 | ||
| HIPAA Controls and Compliance | 00:07:00 | ||
| Roles and Responsibilities | 00:10:00 | ||
| Manage Communication and Ethics Issues | 00:15:00 | ||
| Legal Best Practices, Requirements, and Documentation | 00:09:00 | ||
| Medical Document Imaging | 00:04:00 | ||
| Sanitation Management | 00:02:00 | ||
| Computing Essentials | 00:05:00 | ||
| Networking 9988 | 00:32:00 | ||
| Manage Servers and Software | 00:27:00 | ||
| Hardware Support | 00:14:00 | ||
| Set Up a Workstation | 00:08:00 | ||
| Troubleshoot Basic IT Issues | 00:15:00 | ||
| Troubleshoot Medical IT Issues | 00:19:00 | ||
| Implementation of an EMR EHR System | 00:34:00 | ||
| Change Control | 00:07:00 | ||
| Manage Physical and Logical Security | 00:36:00 | ||
| Implement Security Best Practices and Threat Mitigation Techniques | 00:13:00 | ||
| Manage Remote Access | 00:06:00 | ||
| Manage Wireless Security | 00:14:00 | ||
| Perform Backups and Disaster Recovery | 00:18:00 | ||
| Mock Exam | |||
| Mock Exam – IT Administrator Diploma | 00:30:00 | ||
| Final Exam | |||
| Final Exam – IT Administrator Diploma | 00:30:00 | ||
| Recommended Materials | |||
| Workbook – IT Administrator Diploma | Unlimited | ||
| Assignment | |||
| Assignment – IT Administrator Diploma | Unlimited | ||
| Order Your Certificate | |||
| Order your Certificate QLS | 00:00:00 | ||
Course Reviews
Frequently asked questions
Can’t find the anwser you’re looking for ? Reach out to customer support team.
There are no specific prerequisites for this course, nor are there any formal entry requirements. All you need is an internet connection, a good understanding of English and a passion for learning for this course.
You have the flexibility to access the course at any time that suits your schedule. Our courses are self-paced, allowing you to study at your own pace and convenience.
For this course, you will have access to the course materials for 1 year only. This means you can review the content as often as you like within the year, even after you've completed the course. However, if you buy Lifetime Access for the course, you will be able to access the course for a lifetime.
Yes, upon successfully completing the course, you will receive a certificate of completion. This certificate can be a valuable addition to your professional portfolio and can be shared on your various social networks.
We want you to have a positive learning experience. If you're not satisfied with the course, you can request a course transfer or refund within 14 days of the initial purchase.
Our platform provides tracking tools and progress indicators for each course. You can monitor your progress, completed lessons, and assessments through your learner dashboard for the course.
If you encounter technical issues or content-related difficulties with the course, our support team is available to assist you. You can reach out to them for prompt resolution.





 LOGIN/Sign up
LOGIN/Sign up





Gabriel Santos
A great course and a must to-be-taken course for IT experts to explore the administration panel and standards.
Kevin Hyman
Outstanding thing to get in-depth understanding of the ITs and developer basics. Also imp to do othr assignmnts
Josephine Gunderson
Good news for no IT students. Good course in cheap
Kevin Wojcik
Should be more detailed about spywares. how to remove and gow to get rid of it
Maria Beyer
so much information on the host security panel. otherwise very well organised and very much updated. um happy
IT Administrator Diploma
Great, Recommended